Conquer Mission 6: The Network in Intravenous 2. Infiltrate, disrupt enemy communications, and gather vital intel for Act 2.
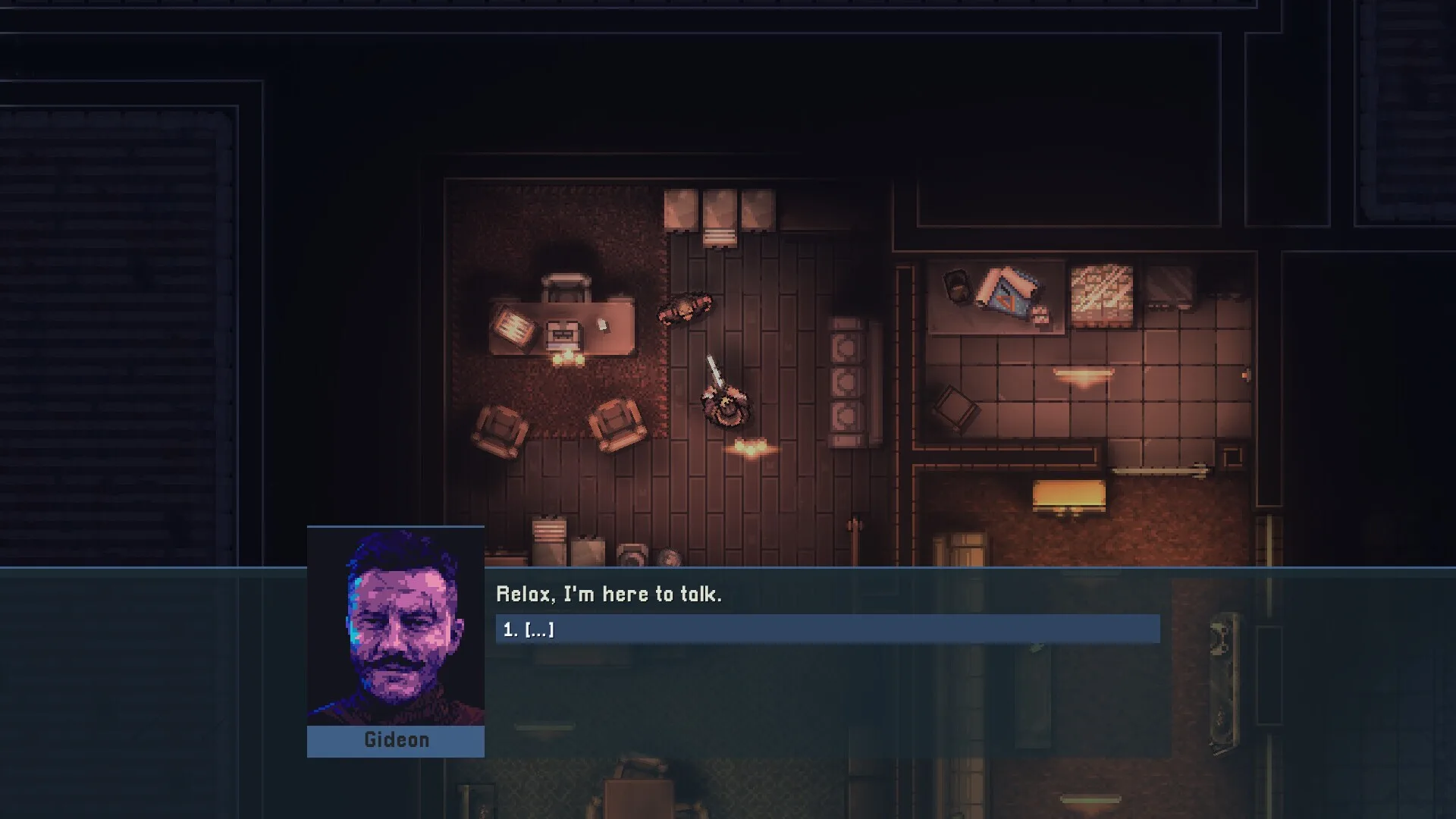
Mission 6: The Network is a pivotal point in Act 2: The Pursuit of Intravenous 2: Mercenarism. This mission often involves disrupting or exploiting an enemy communication or data network, crucial for advancing your objectives. Success here can provide vital intelligence or cripple enemy operations.
Mission Objectives
Your primary goal in Mission 6 is to infiltrate a secure facility housing a critical network infrastructure. This could involve disabling enemy servers, stealing sensitive data, or planting a virus. The mission will likely feature advanced security measures, including electronic countermeasures, surveillance systems, and elite guards.
Infiltration Strategies
Given the nature of a network facility, stealth is often paramount. Look for opportunities to bypass security checkpoints, disable cameras, and jam communications. You might need to find access codes, hack terminals, or use specialized gadgets to overcome electronic defenses. Consider the following approaches:
- Silent Takedowns: Neutralize guards discreetly to avoid raising alarms.
- Environmental Hacking: Interact with terminals to disable security or open new paths.
- Distraction Tactics: Use noise makers or environmental hazards to lure guards away from their posts.
- Ventilation Systems: Explore alternative routes through vents for stealthy traversal.
Combat Encounters
While stealth is ideal, you should always be prepared for combat. The network facility will likely be defended by well-trained personnel. Expect encounters with:
- Standard Security: Armed with assault rifles and pistols.
- Heavy Troopers: Equipped with body armor and heavier weaponry.
- Specialized Units: Potentially including snipers or combat engineers.
use cover effectively, aim for critical hits, and manage your ammunition and health carefully. If alarms are triggered, be ready to adapt to a more aggressive engagement.
Key Locations and Items
Within the network facility, you'll likely encounter server rooms, control centers, and administrative offices. Keep an eye out for valuable intel, keycards, or hacking tools that can aid your progress. The main objective terminal or server will be heavily guarded, requiring a final push to complete the mission.
Tips for Success
- Scout the area thoroughly before committing to an approach.
- Prioritize disabling surveillance systems to reduce the risk of detection.
- If hacking is involved, ensure you have enough time and cover to complete the process.
- Be prepared for a potential extraction or escape sequence after completing the primary objective.
100% Human-Written. AI Fact-Checked. Community Verified. Learn how AntMag verifies content