Navigate Mission 2: The Investigation in Intravenous 2: Mercenarism. Gather crucial information and piece together the first clues in Act 1, The Awakening.
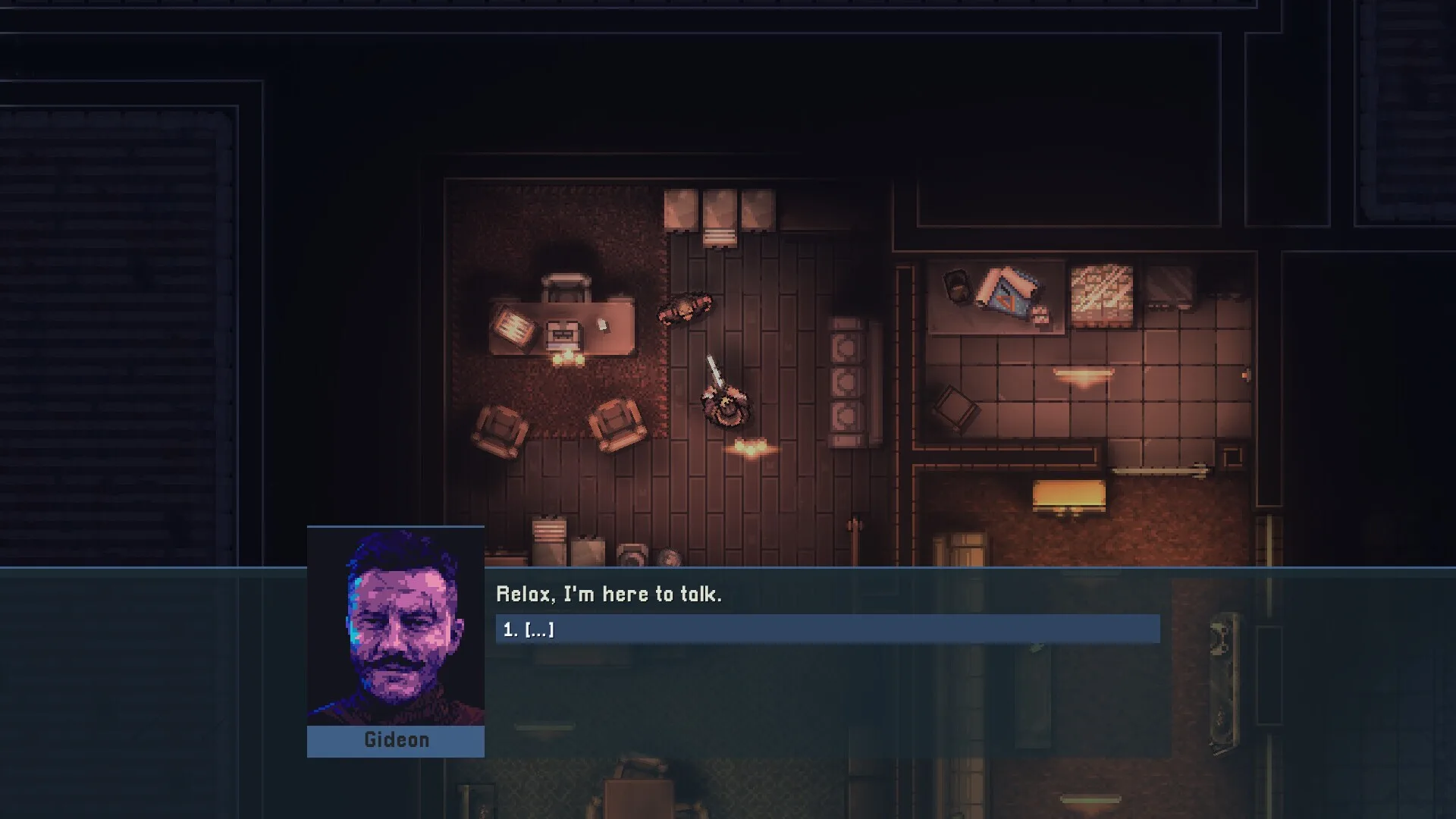
Mission 2: The Investigation, marks the beginning of Gideon's deep dive into the conspiracy in Act 1: The Awakening. This mission focuses on gathering crucial information and piecing together the initial clues.
Mission Overview
Following the initial contract, Gideon realizes there's more to the situation than meets the eye. Mission 2 tasks you with infiltrating a location to gather evidence, interrogate key individuals, or recover sensitive data that sheds light on the true nature of the conspiracy. Expect a blend of stealth, combat, and puzzle-solving elements.
Infiltration and Exploration
The mission typically begins with Gideon needing to gain access to a restricted area. This could be an office building, a research lab, or a secure data center. Stealth is often encouraged in the initial stages to avoid raising alarms and to gather information without immediate confrontation. Look for ventilation shafts, alternate entry points, or opportunities to disable security systems.
Gathering Intel
Your primary objective is to find specific pieces of information. These can be found in various forms:
- Documents and Files: Often found on desks, in filing cabinets, or on computers.
- Audio Logs or Recordings: Provide spoken clues and context.
- Computer Terminals: May require hacking or finding passwords to access sensitive data.
- Interrogations: You might need to confront and extract information from specific NPCs.
Pay attention to highlighted objects and interactive elements in the environment.
Combat Encounters
While stealth is often preferred, you will inevitably encounter resistance. Security guards, corporate enforcers, or even rival mercenaries may be present. These encounters can range from small patrols to larger firefights. Be prepared to switch to combat mode if stealth fails or if a direct approach is necessary to access certain areas.
Key Locations and Objectives
- Reception Area: Often the first point of entry, may contain initial clues or security personnel.
- Server Room/Data Center: A common location for critical data retrieval, usually heavily guarded.
- Executive Offices: May contain personal files, encrypted messages, or lead to key individuals.
- Research Labs: Could hold experimental data or evidence of illicit activities.
Strategic Tips
- Use Your Gadgets: Deploy distractions, EMP devices, or hacking tools to bypass security and neutralize guards.
- Observe Patrols: Before moving, take time to observe enemy patrol patterns to find safe windows for movement.
- Prioritize Objectives: Focus on gathering the required intel. Side objectives can be pursued if time and resources allow.
- Weapon Choice: A silenced weapon is highly recommended for stealth. If combat is unavoidable, have a reliable weapon for direct engagement.
Successfully completing Mission 2: The Investigation is vital for understanding the unfolding plot and preparing for the challenges ahead in the Mercenarism campaign.
100% Human-Written. AI Fact-Checked. Community Verified. Learn how AntMag verifies content