Confronting the rogue hacker in Solarpunk requires advanced cybersecurity measures, including AI threat analysis and digital counter-espionage units.
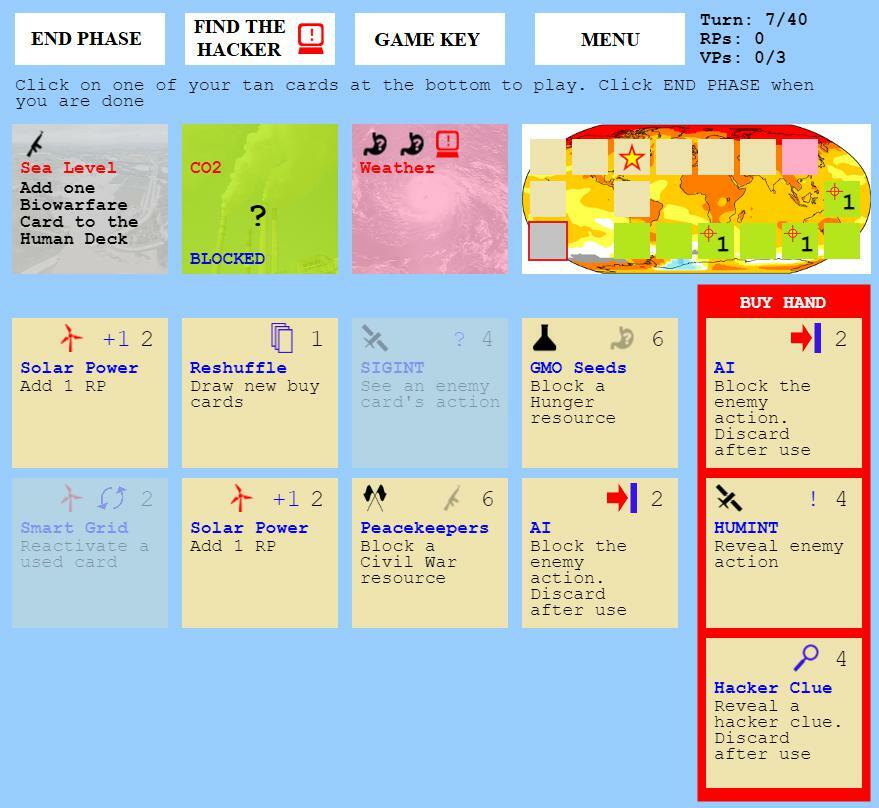
The emergence of a rogue hacker entity presents a unique and formidable challenge within Solarpunk™. This adversary operates outside the established societal structures, utilizing digital means to disrupt progress, steal data, and sow chaos. Confronting this threat requires a specialized approach, focusing on cybersecurity, digital forensics, and the development of counter-hacking measures. invest heavily in their digital defense infrastructure, train specialized cyber warfare units, and potentially engage in a high-stakes digital cat-and-mouse game to track down and neutralize the hacker's operations. The success of this endeavor is crucial for maintaining the integrity of your systems and protecting the hard-won gains of your sustainable civilization.
The hacker represents a modern form of threat, one that preys on the interconnectedness of your Solarpunk™ world. Their attacks can cripple vital infrastructure, compromise sensitive research data, and undermine public trust. To overcome this, players must not only bolster their digital defenses but also understand the hacker's motives and methods. This might involve tracing their digital footprints through complex networks, identifying their vulnerabilities, and developing sophisticated countermeasures. The game mechanics at this stage often introduce new research trees focused on advanced encryption, AI-driven threat detection, and digital counter-intelligence. Successfully neutralizing the hacker is a testament to the resilience and adaptability of your civilization in the face of novel, technologically driven threats.
Cybersecurity Measures and Counter-Hacking
- Invest in Advanced Firewalls and Intrusion Detection Systems: Upgrade all network nodes with the latest security protocols to detect and block unauthorized access attempts.
- Develop AI-Powered Threat Analysis: Research and deploy artificial intelligence systems capable of identifying anomalous network behavior and predicting potential attack vectors.
- Establish a Dedicated Cyber Warfare Division: Train and equip specialized units focused on offensive and defensive cyber operations, including digital forensics and counter-espionage.
- Implement Multi-Factor Authentication: Secure all critical systems and data repositories with robust authentication methods to prevent unauthorized access.
- Regularly Patch and Update Systems: Ensure all software and hardware are kept up-to-date with the latest security patches to close known vulnerabilities.
Tracking and Neutralizing the Hacker
- Digital Footprint Analysis: Utilize forensic tools to trace the hacker's digital activities across networks, identifying their origin points and operational bases.
- Decoy Networks and Honeypots: Set up simulated vulnerable systems to lure the hacker into revealing their tactics and compromising their anonymity.
- Develop Counter-Exploits: Research and create digital tools designed to exploit vulnerabilities within the hacker's own systems or communication channels.
- Coordinate Digital and Physical Raids: If the hacker's physical location is identified, coordinate with ground forces for a swift and decisive apprehension.
Potential Hacker Tactics and Motivations
- Data Theft: The hacker may aim to steal proprietary research data, economic strategies, or personal information of key figures.
- Infrastructure Sabotage: Attacks could target power grids, communication networks, or automated production lines, causing widespread disruption.
- Information Manipulation: The hacker might spread disinformation or alter critical data to incite panic or distrust among the population.
- Extortion: A common motive could be demanding payment in cryptocurrency or resources in exchange for ceasing attacks.
100% Human-Written. AI Fact-Checked. Community Verified. Learn how AntMag verifies content